Scanning the ports of a Windows machine
As part of a troubleshooting or security audit, it may be interesting to know which ports are open by which applications on a host. We’ll see in this article how it can be done using simple tools.
We will try to make use only of windows-integrated tools or Microsoft-provided.
Netstat
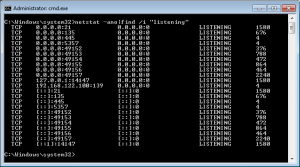
Netstat is an Windows-integrated program that allows you to list open ports on your local host. To see which ports are open (listening), just type the command:
netstat -ano |find /i "listening"
The result is displayed in the form of columns: the protocol, the host with its port, the destination with its port, state (listening, established, …) and the PID of the process (-o option)
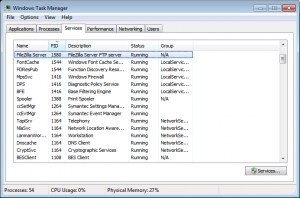
The application in question can be easily identified with the PID found in Task Manager (taskmgr.exe) or in the Tasklist program.
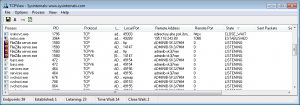
TCPView
Similar to netstat the NetView utility displays the same information but on a graphical interface. It requires no installation and can be used directly after downloading it on the Microsoft Sysinternals website:
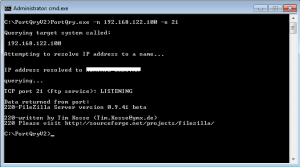
PortQuery V2
PortQuery can scan local but also remote ports. Local ports can be analyzed using the following command:
portqry -local
While to analyze a remote machine, you must specify the IP address or hostname and the ports to scan:
portqry -n hostname -r 100:150
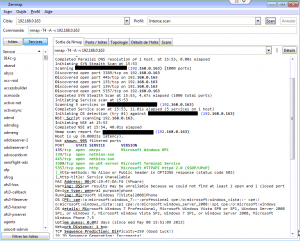
NMAP
The preferred tool of pirates and security auditors. Nmap is by far the most powerful and complete free tool. Using the command line or the Zenmap GUI, it allows port scanning in a fast and complete way, and has many other functions. Supported by a very active community, it is present on a wide variety of platforms, including Windows. Here is an example of a scan on a Windows machine:
Conclusion
Small utilities such as netstat and portqry are very useful to quickly identify a problem or make troubleshooting, but if you are doing security audits, they are lacking a lot of functions. If you want a full audit of your infrastructure, Nmap is the perfect tool.
Trackback from your site.